How To Find and Hire an Ethical Hacker
Learn how to hire ethical hackers to protect your business from cyber threats. Discover types of services, qualifications to look for, and legal considerations.

Cybersecurity threats are on the horizon. As they grow more sophisticated, many businesses turn to ethical hackers to help.
Whether you're a small business owner, a large corporation, or someone who manages sensitive data, an ethical hacker can be an incredible asset. That’s why the penetration test market is set to hit $12.76 billion by 2029.
But how do you find the right expert? This guide will help you find and hire the perfect ethical hacker.
What is an ethical hacker?
Ethical hackers enhance a company's digital security by identifying and addressing vulnerabilities before malicious actors exploit them. Unlike black-hat hackers, who aim to cause harm, ethical hackers safeguard businesses by anticipating potential threats.
These security professionals:
- Conduct comprehensive assessments
- Perform penetration tests
- Advise teams
- Fortify systems.
Rather than compromising data or finances, ethical hackers bolster an organization's online defenses. They meticulously examine computer systems, networks, and websites for weaknesses.
By doing so, ethical hackers help companies comply with industry standards, mitigate cybersecurity risks, and foster customer trust in their digital infrastructure.
Why would a business need ethical hackers?
Businesses need ethical hackers to stay safe from evolving cyber threats. With the rise of AI, many business models are taking a more digital approach. These trends make small businesses focus more on growth and less on security.
Here's why ethical hackers are important:
1. Growing cybersecurity threats
There seem to be new digital threats every day. Hackers use sophisticated techniques like phishing and malware to steal information from individuals and businesses. In October 2023, Sav-Rx suffered a cyberattack that exposed 2.8 million people's data, including social security numbers, addresses, and more.
2. Proactive security measures
Ethical hackers find and fix vulnerabilities before malicious actors exploit them, and regular testing keeps defenses strong against new threats.
3. Compliance requirements
Industries have strict security regulations. Ethical hackers help businesses meet these standards, avoiding fines and legal issues. They assist in complying with GDPR, HIPAA, and other laws.
4. Protect brand reputation
A security breach can instantly damage a brand's reputation. Ethical hackers prevent breaches that erode customer trust and relationships.
How to hire qualified ethical hackers
Learning how to hire ethical hackers starts with identifying your cybersecurity needs and researching qualified professionals. Here are the steps to take:
1. Assess your needs
Determine which areas of your business are most vulnerable or critical. For example, a financial services company might prioritize payment processing system security, while a tech startup may focus on protecting intellectual property.
Decide whether you need:
- A vulnerability assessment to identify security gaps.
- A comprehensive penetration test that simulates real-world attacks.
- Specialized testing for new mobile apps or cloud infrastructure.
Consider whether a one-time assessment or ongoing security monitoring is necessary. Your needs will dictate how much you’ll spend on cybersecurity services.
2. Look for qualified hackers
There are four main ways to find a qualified ethical hacker:
- Online platforms
- Professional networks and associations
- Cybersecurity conferences
- Referrals
Online platforms
Marketplaces make it easy to hire external consultants. They connect you with experienced digital security professionals, like hackers, for one-time consultations and ongoing support.
You can find an ethical hacker in a few different ways on Fiverr:
Search and browse
Type specific phrases like “digital security” or “penetration testing” into the search bar on Fiverr’s homepage.

Another option is to browse by category. Head to the Programming & Tech category, then click into the “Cybersecurity” subcategory.
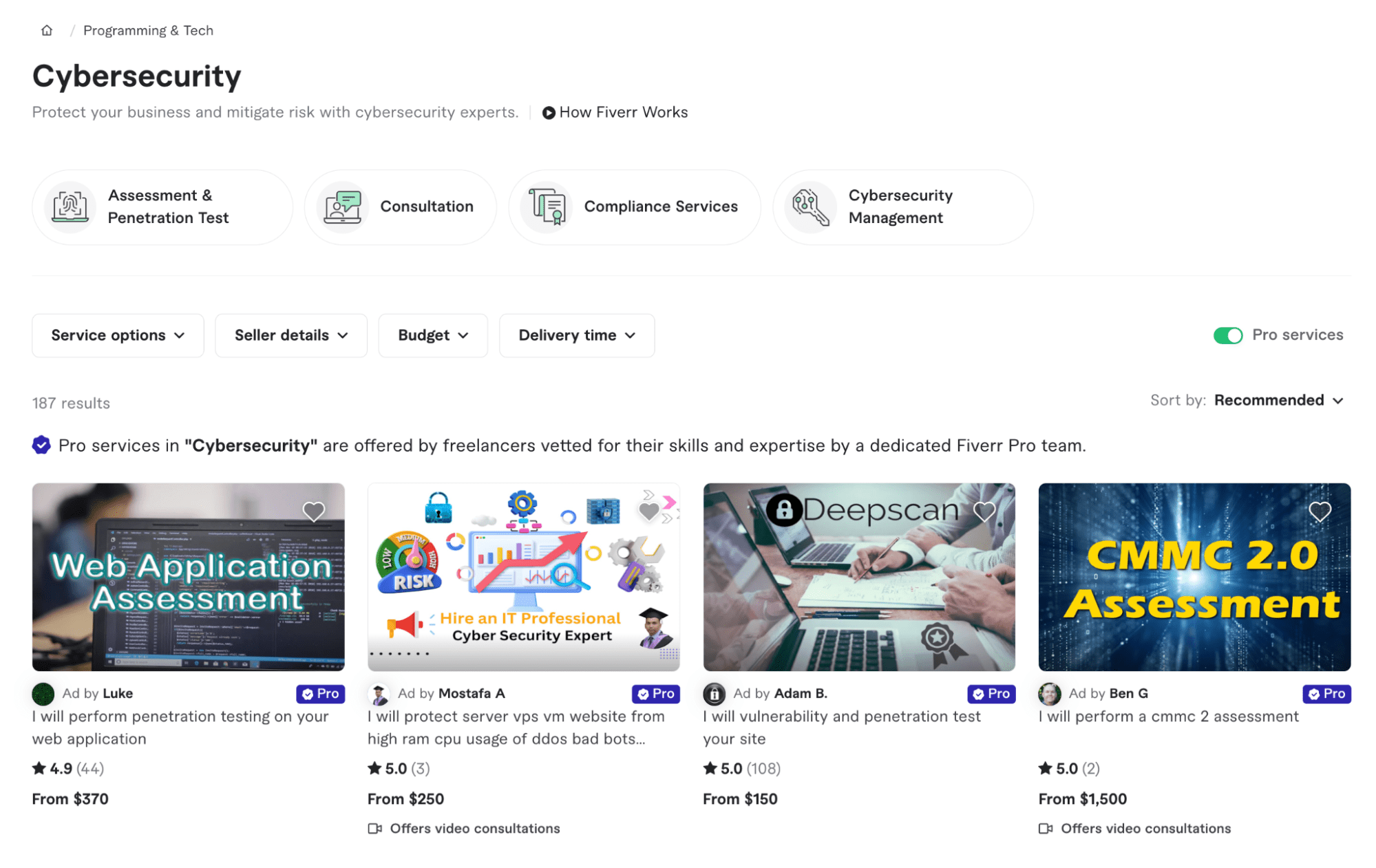
💡Tip: Refine your search results using filters such as seller level, location, budget, and delivery time to find the right digital security specialist.
Post a request
Public a brief describing the digital security services you need. Sellers who offer similar services can respond to it with custom offers. Fiverr helps you create a brief using AI to include fields for a project goal, scope of work, and required expertise.

Neo, Fiverr AI agent
Neo, Fiverr's AI agent, streamlines the process of hiring the perfect ethical hacker. The system asks targeted questions and gathers details about your needs and budget. Then, Neo identifies the best freelancer for your needs.
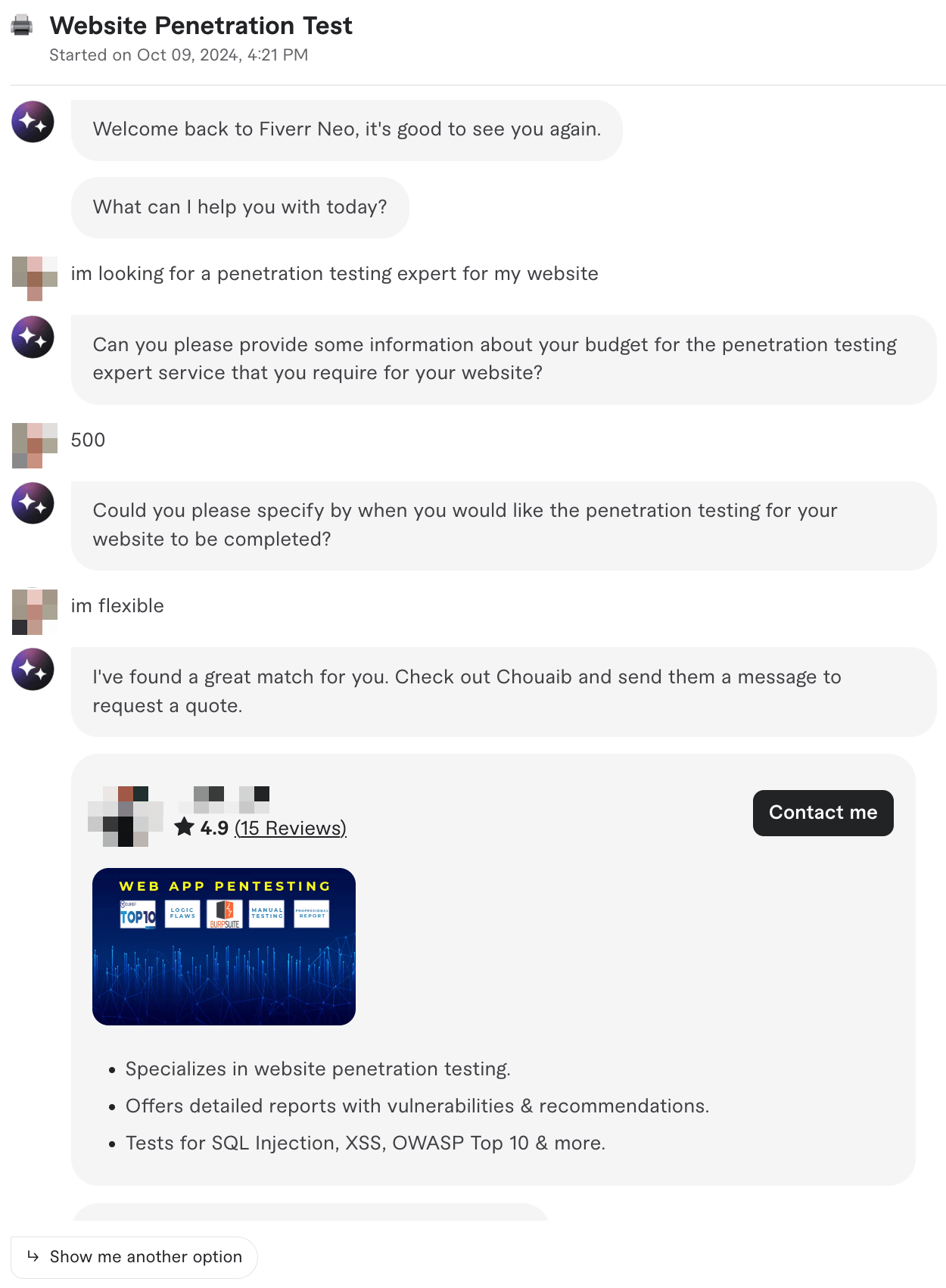
If you like the recommendation, click the “Contact me” button, and Neo will generate a message to send to the freelancer.
Professional networks and associations
Professional networks and associations offer another effective avenue for finding qualified, ethical hackers. Reputable organizations like EC-Council (CEH) and (ISC)² (CISSP) maintain directories and job boards featuring skilled professionals who adhere to strict ethical standards.
These networks connect businesses with trustworthy cybersecurity experts and provide opportunities to interact at industry events and forums.
Cybersecurity conferences and events
Cybersecurity events are also great for finding top-tier ethical hackers.
Consider the following:
- Major industry gatherings like DEF CON, Black Hat, and the RSA Conference offer excellent opportunities to connect with leading ethical hackers.
- Engage with speakers, workshop leaders, and fellow attendees to identify potential candidates.
These events often feature job fairs and networking sessions to help employers connect with cybersecurity professionals.
Referrals
Referrals from trusted businesses or IT experts are a great way to find an ethical hacker. Hackers recommended by trusted sources are skilled and reliable.
Ask your professional network—coworkers, IT service providers, and clients—if they know anyone you could hire. The hacker's previous customers provide useful referrals.
3. Screen job candidates
Screening qualified, ethical hackers ensures they fit your company's values and needs. Check their CEH, OSCP, or CISSP credentials, work experience, and problem-solving skills. Browse their portfolio for relevant case studies and work. Focus on how they handled similar issues.
Fiverr's detailed seller profiles and service descriptions help you identify contractors with experience that matches your needs. For example, you can see in the Seller profile below that the ethical hacker holds an OSCP certification, a BSs in Ethical Hacking, and has years of experience in penetration testing.
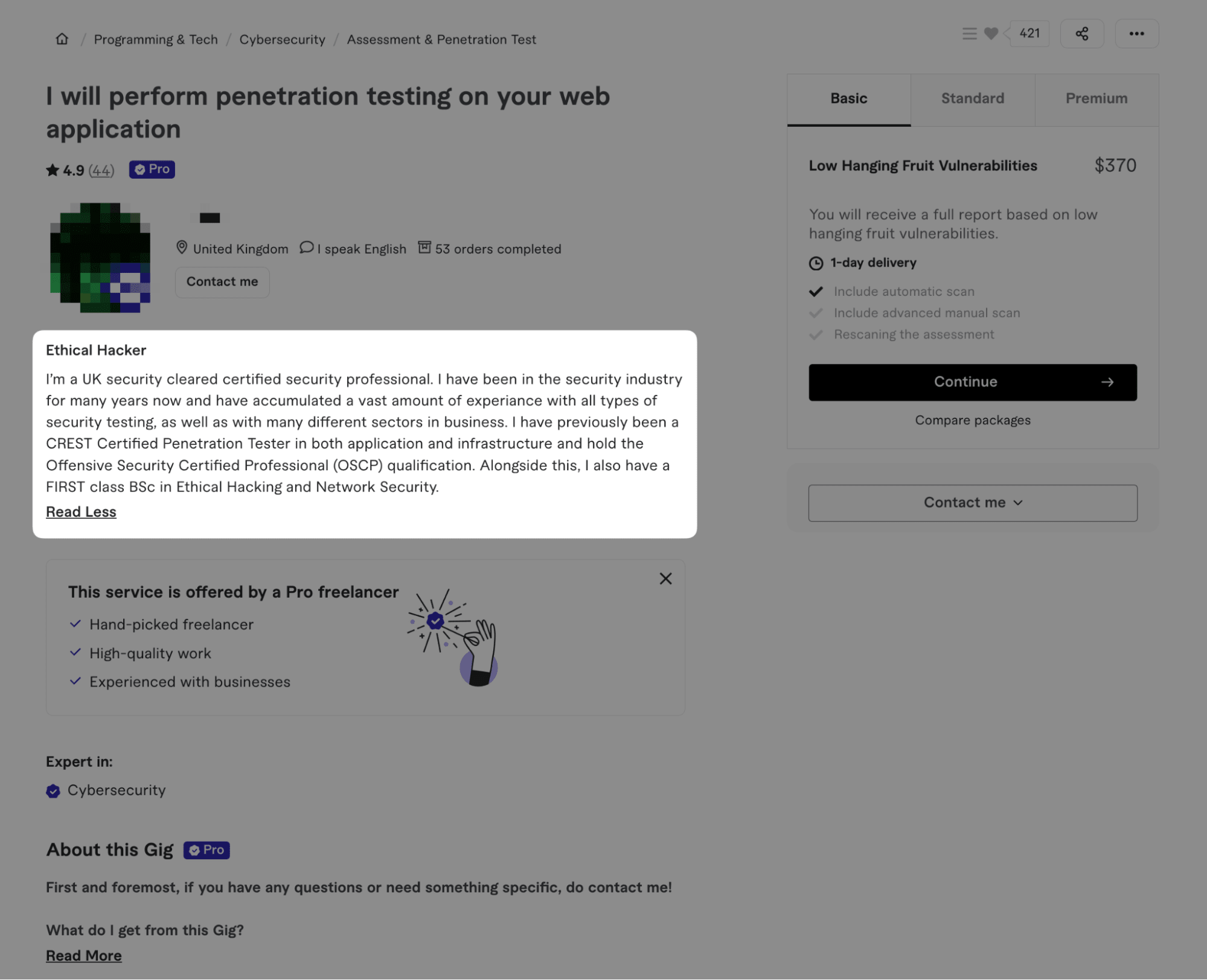
Next, interview them for technical skills to see how well they know the job and can simplify complex ideas. On Fiverr, you can easily communicate with multiple security professionals to assess their responses before deciding through a messaging system. Sometimes, a phone screening is helpful to speed up the process.
4. Compare and evaluate potential hackers
After researching security professionals, compare and contrast them. Evaluate how each candidate answered your inquiries. Were their responses confident, clear, and informative?
Ask for references and read reviews to see what others think. Fiverr lets you see ratings and reviews on a Sellers profile to help you make a better decision.

Check each candidate’s prices and services. Some offer all-inclusive security packages, while others charge per task.
Fiverr makes this comparison easy by providing clear, upfront pricing and service descriptions for each security professional. You can quickly compare different packages and find one that fits your budget and needs.
Lastly, choose a security professional with case-specific experience. An expert who knows everything about network security, penetration testing, and compliance can make a big difference.
Fiverr's search filters and detailed seller profiles can help you find security professionals with expertise in your specific situation, whether it's personal cybersecurity, business security, or specialized areas like IoT security
5. Make the offer and onboard
When choosing a security professional, balance your instincts with their qualifications, focusing on someone who can address both current and future security needs.
Before committing, carefully review the engagement terms, paying close attention to offered services, fees, and confidentiality clauses. Set clear expectations for communication and workflow from the outset.
Fiverr simplifies the process of finding and hiring the right security expert. To maximize your experience:
- Thoroughly review service descriptions and client feedback
- Utilize Fiverr's messaging system to clarify any expertise-related questions
- Leverage the platform's built-in protections, including payment holds and dispute resolution
- Clearly articulate your specific security requirements when placing an order
Remember that complex security challenges often demand ongoing, personalized attention beyond a single gig.
By carefully weighing these factors and using Fiverr's safeguards, you can confidently select a security professional and establish a solid foundation for a productive working relationship.
Types of ethical hacking services
Understanding how to hire a professional hacker involves more than finding someone with technical skills. Ethical hacking uses multiple techniques to fix specific problems in your systems that you must be aware of.
Knowing which type of service your business needs is crucial to building a robust cybersecurity strategy.
Vulnerability assessments
Vulnerability assessments act as comprehensive health checks for IT infrastructure. Ethical hackers thoroughly examine systems to find security gaps and potential entry points for attackers. They provide detailed reports with actionable recommendations to strengthen defenses.
Penetration testing
Penetration testing goes a step further by simulating real-world cyberattacks. Hackers attempt to exploit vulnerabilities in networks, applications, and even physical security measures. This reveals how far an attacker could infiltrate systems and access sensitive data.
Social engineering tests
Social engineering tests focus on the human element of security. By using tactics like phishing emails and false scenarios, ethical hackers evaluate how employees respond to manipulation attempts. This helps identify areas where staff need additional security awareness training.
Web and mobile application security testing
Web and mobile application security testing has become increasingly crucial. Ethical hackers search for common vulnerabilities like SQL injection and cross-site scripting in web apps, while also examining mobile apps for data leakage and insecure storage issues. These tests are vital for protecting user data and maintaining trust.
Cloud security assessments
Cloud security assessments have become more important as businesses migrate to the cloud. These evaluate the security of various cloud service models to ensure data remains protected in these environments.
IoT device testing
IoT device testing addresses the unique challenges posed by the Internet of Things. Hackers examine these devices for weak passwords, insecure protocols, and firmware flaws that could compromise network security.
Legal considerations and contracts
Legal considerations are crucial when engaging an ethical hacker. Obtain proper authorization through written consent and a scope of work agreement. Ethical hackers should sign an NDA to protect private data. Stay compliant with relevant laws and regulations:
- Computer Fraud and Abuse Act (US)
- Industry-specific rules (e.g., HIPAA, PCI DSS)
- Cross-border data testing regulations
Protect sensitive data during testing by minimizing exposure, implementing encryption, and establishing clear handling policies. Handle critical vulnerabilities promptly:
- Immediate reporting of major security holes
- Detailed documentation of vulnerabilities
- Follow-up actions with set deadlines
Fiverr simplifies the process by offering vetted professionals. When drafting contracts, specify tests, define scope, and protect both parties' interests. Remember to follow local, national, and international cybersecurity laws. This approach helps navigate the legal landscape while securing your systems effectively.
Hire a certified ethical hacker on Fiverr today
Explore Fiverr's range of ethical hacking and cybersecurity experts to find the right professional for your business needs. Join Fiverr and access a marketplace of talented and vetted freelancers.
Hackers for hire FAQ
Is hiring a hacker legal?
Yes, if you hire a good hacker who doesn’t have a shady background and is not involved in illegal activities. Ethical hackers, or white-hat hackers, test and secure systems. Following a strict code of ethics, they work within the law to find and fix security weaknesses.
Can you hire ethical hackers?
Absolutely, you can hire ethical hackers. Ethical hackers identify security threats before they become problems. They use the same methods as bad hackers, but with your permission and to improve security. Find ethical hackers on Fiverr, in professional networks, or through business recommendations.
How much do companies pay for ethical hackers?
Ethical hackers' pay depends on experience and industry. Ethical hackers start at $60,000–$80,000. As they gain experience, middle-level professionals can earn $90,000–$130,000.